RSAC Founder Festival 2026: Thank You!


Today, we’re excited to announce our investment in Mallory, an AI-native threat intelligence platform.
In the agentic era, attackers no longer operate at human speed. They use AI to discover vulnerabilities, chain exploits, and execute attacks faster than defenders can reason about them. Meanwhile, most threat intelligence platforms were built for a different time, one defined by manual analysis of feeds, dashboards, and reports. That model is breaking.
Security teams don’t have a data problem; they have a context problem. They’re flooded with signals but lack clear answers to what actually matters: what’s exploitable, are we at risk, and what should we fix right now?
Mallory flips this paradigm. It ingests global threat data, maps it to an organization’s real environment, and uses AI to generate prioritized, evidence-based answers, not more alerts, but actionable intelligence.
Founded by former Google and Mandiant leader Jonathan Cran, Mallory represents a new approach to modern security.We sat down with Jonathan to talk about his vision for Mallory in our founder Q&A:
I grew up on a farm in Iowa — a very classic Midwest childhood. The first computer I had access to was there because of the farm, mostly for operational and financial stuff, but it quickly became something else for me: a portal to the Internet.
My mom worked for Iowa State University at the time, and through that I got access to early online BBSes. That was the hook. When we got hooked up at home, I spent a ton of time exploring these weird, fascinating communities and finding IRC channels to learn more and more about programming and hacking.
I’ve also always been entrepreneurial. My first business was when I was eight — we’d plant sweet corn and in the summer, put up a big plywood sheet that said three bucks for a dozen ears. I was always trying to build things, even before I had the language for it.
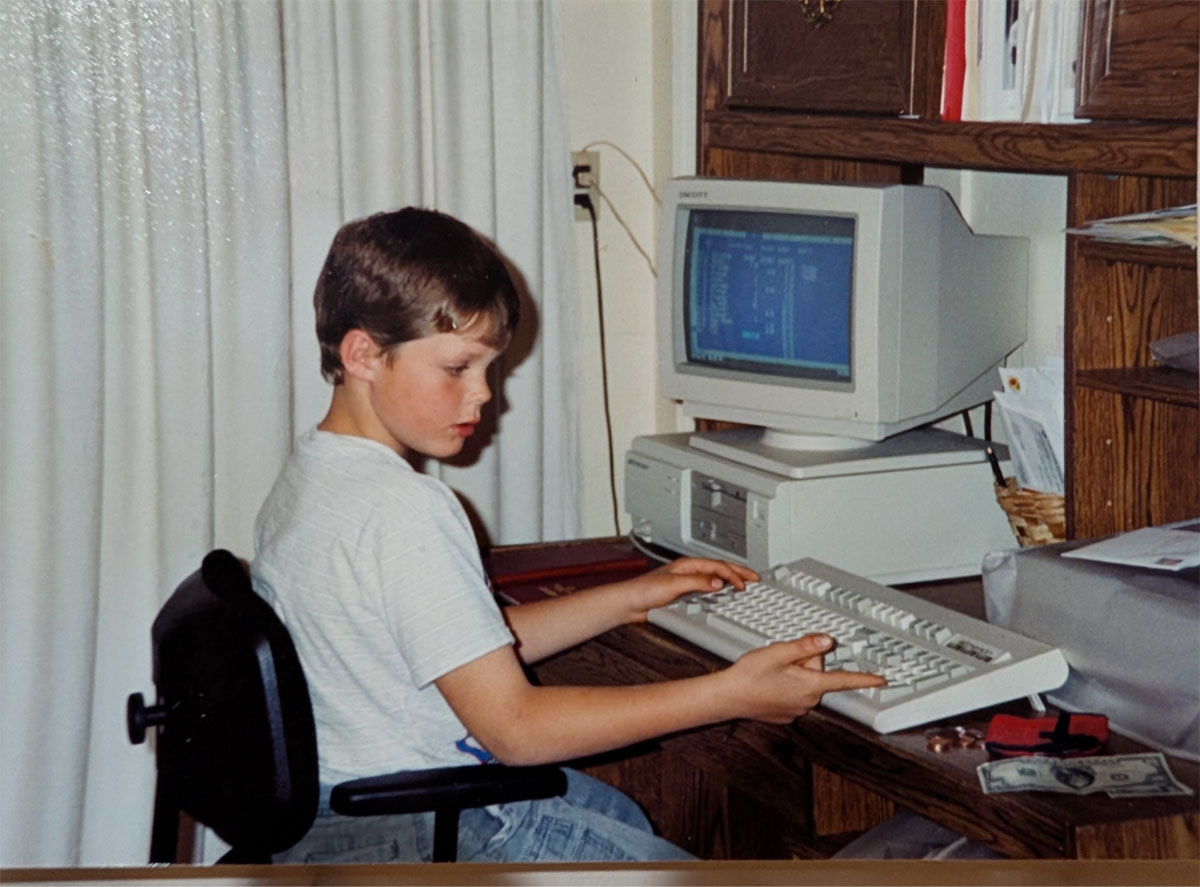
Games were the first thing that really pulled me into computers - Commander Keen and other early shareware were the gateway drug. But the path into security was more accidental, and it started with how open universities were back then.
As soon as I got to university I took a help desk job that quickly turned into network administration for one of the colleges. This was the early 2000s — there were no network firewalls, and SMB protocol worms (Sasser, Blaster, etc) were a formative experience - these bugs would take down huge numbers of machines in minutes.
The process of learning how these bugs worked, understanding the attack and learning how to abuse systems and protocols - that was the moment where I realized what I wanted to do.
After university, I knew I wanted to get into cybersecurity professionally… but it wasn’t really a defined job path yet. I was told to stick with IT, but I just couldn't learn enough. I interviewed at a few places, Symantec, and boutique consulting shops, but then I flew up to Boston and interviewed at Rapid7.
What struck me about Rapid7 wasn’t just the work — it was the energy. They were early, loud, moving fast. I joined in 2007 and went straight into pentesting. It was the kind of environment where you learn by doing: you’re thrown into real engagements, learning on the fly, traveling constantly. It was 80% travel for years. Straight out of school you don’t care — you’re happy to get on a plane and go break into a bank.
One of the most memorable engagements I ever did was for a jeweler in New York. We didn’t realize at the time that they were going out of business, so everyone was already on edge. We did a combined physical and network engagement… they had incredible loss prevention so cameras everywhere. We got Domain Admin the first day after cracking the weak (WEP) wireless networks.
When I went to do the physical testing that evening I was met by a gentleman holding a baseball bat! Needless to say, we did the rest of the test from a coffee shop down the street. It was a success, I suppose, but you realize there are many layers to security.
Eventually, though, you start to notice the same techniques working over and over. Past-the-hash, grab domain admin, move laterally — the pattern repeats. And I realized I could have a much bigger impact by building products than by repeating the same engagement loop.
That frustration with the state of cybersecurity is what led me to Metasploit - I ended up pinging HD Moore when Rapid7 acquired the team. I remember the conversation clearly - he spoke so fast I could catch every third word. The only thing I really remember is: “Get down to Austin as quick as you can.”

So I did. It was a team of six sitting in a hotel room building the first iteration of Metasploit Pro - jduck, egypt, todb, sinn3r. Everyone was at the top of their game and put in the work. We spent four years together working hand in hand with the Metasploit community and shipped a ton of product and capability over that time.
I moved from there to Bugcrowd after meeting Casey. Bugcrowd was just getting started and it wasn’t just a software company. It was an entirely different approach to the problem of securing the attack surface. The value was in the community’s ingenuity, and to harness that required real security skills - analyzing and triaging submissions. We were doing triage by hand early on, and then we had to figure out how to scale that. Over time, it became about building a market from scratch — making it acceptable for companies to ask hackers to “punch them in the face.”
By the time I left, 5 years later - the crowd was 100,000 strong. Bug bounty went from “unthinkable” to something Fortune 1000s institutionalized. That experience — the power of community
I took other jobs along the way - Kenna Security was extremely formative and interesting - working with folks like Ed Bellis, Michael Roytman, and Jay Jacobs - learning how ML and AI could be harnessed to help with exposure management. We released the Prioritization to Prediction research series and helped get EPSS off the ground.
But I knew I wanted to build from the ground up.
It started as an open-source project that was almost like “Maltego for proactive security.” The core idea was to pull together many different signals to understand the security posture of an organization from the outside in — what you could see, infer, and validate externally.
We had a vibrant community, and I was gathering a lot of data - I've always loved building collection systems. In 2020 - shortly after the pandemic hit - I remember a friend telling me, “You’re going too slow building this as open source. You need to move faster.” So I raised a little money, put together a small team, and we went.
We were inventing a market while we were building. Early on, people called it “digital risk” or “digital footprinting,” but it quickly became what the industry now calls Attack Surface Management.
The whole idea was: pull signals from every open and closed source you can, and build a cohesive picture, and help organizations understand their exposure and security posture externally.
We talked to the Mandiant leadership team early on and it was clear that they needed help on this front as they were putting together Mandiant Advantage. We knew we were doing something different and valuable and were ready to scale it massively to public company scale, even as a small team. Those early conversations turned into an acquisition about six months later.
Mandiant was three companies in one: a services company, an intelligence company, and a product company. We were on the product side and serviced external customers, but we were adamant about making sure both the intel and services folks had access to it as well. That helped build a lot of relationships.

Then Google acquired Mandiant, and everything scaled 100x again.
At Google, we were able to pull together vastly larger data sources — VirusTotal, Safe Browsing, Google TAG, internal signals — and start building what became Google Threat Intelligence two years later.
It was an incredible period: the amount of data, the range of capabilities, the potential scale of impact. But the deeper lesson was also clear: in big organizations, even with all the data in the world, getting the right information to the right place at the right time is still painfully hard.
And that’s the real problem.
Security doesn’t fail because we don’t have information. It fails because information is locked behind silos, workflows, and human bottlenecks — and because intelligence without actionability doesn’t matter.
We’re living through an explosion of intelligence: OSINT, underground sources, commercial feeds, internal telemetry. There’s more information than ever.
But it’s impossible for security teams to keep up. They’re expected to do everything: threat hunting, response, alerting, vulnerability management, detection engineering — while the attack surface expands aggressively and the labor pool can’t scale with it. Humans need to sleep.
So threat intelligence as a category hasn’t failed because it lacks depth. It’s failed because it can’t be operationalized at the speed and scale modern environments require.
That’s where agents come in.
Agents can do the work humans can’t do consistently: continuously process, correlate, investigate, and act. But agents are only as effective as the context they have. If data is siloed, agents fail the same way humans do.
Mallory exists to solve that.
Mallory is an analysis and security reasoning engine that enables cyber defenders to know what’s going on in their environments, and take action on it.
We pull together a ton of signal: open sources, underground intelligence, commercial feeds — and then connect that to what matters inside an organization. The goal is to build a cohesive picture of what’s happening and how it’s relevant to you.
From there, we contextualize and prioritize: if an attacker is targeting you, how are they targeting you? What techniques and behaviors matter? What controls do you need to tune? What actions should you take?
It’s not enough to “have intelligence.” You need intelligence that is actionable, delivered, and operationalized.
We’re building a better, more proactive, future for security operations teams - imagine a world that has near real-time information about new threat techniques, exposures, compromises and well-harnessed intelligent agents to check and manage that posture against new information. It’s early but you can see glimmers of an un-siloed intelligence layer that integrates external signal and internal business context.
A concrete way to think about it: every week, sometimes every day, there’s a new “Shellshock moment.” A new vulnerability drops, and organizations scramble. Today, responding requires days of manual work: check Jamf for endpoints, Wiz for production, GitHub for pre-production, asset databases, ticketing systems. You’re stitching together a picture across dozens of systems.
An agent is able to do that investigation in seconds: find where it exists, how exposed it is, who owns it, and what needs to happen next. On the reactive side, it’s similar. New attacker behavior emerges. Do we have detections for it? Where should we detect it — web, endpoint, cloud? Are detections in sync across an expanded detection surface?
Mallory helps answer those questions contextually and continuously — and makes sure the right action happens, not just the right report gets written.